Introduction: How to Recover from a Ransomware Attack
Ransomware attacks are one of the most common and harmful cybersecurity threats faced by individuals and businesses today. These attacks can render your files inaccessible and demand a ransom, typically paid in cryptocurrency, for their release. The good news is that you can recover from a ransomware attack, but it requires careful, informed action.
This guide will walk you through 20 detailed steps for how to recover from a ransomware attack. These steps will help you understand the process, from disconnecting your infected devices to securing your data for the future.
Step 1: Disconnect Your Gadgets from the Network Right Away– Vital for How to Recover from a Ransomware Attack

When you initially presume a ransomware attack, detaching your infected device from the web and your regional network is your very first top priority. This action is absolutely crucial to avoid the ransomware from infecting other devices or encrypting extra files. By disconnecting, you’re buying yourself time to find out what occurred without intensifying the circumstance. This is a vital part of recover from a ransomware attack.
Why Disconnecting is Crucial in the Ransomware Recovery Plan
Ransomware doesn’t just rest on your device quietly. It is designed to spread and encrypt files throughout your network. Lots of ransomware pressures search for connected gadgets or drives to infect, causing more damage the longer they have access to your system. If you take speedy action to isolate the contaminated gadget, Ransomware disaster healing is just possible.
If your contaminated laptop computer stays connected, the ransomware can spread to your desktop computer, external drives, or even shared folders on the network. The goal of detaching is to stop the ransomware from continuing to spread out and secure more files, conserving your data from further damage and contributing to your ransomware disaster recovery.
How to Disconnect: A Practical Guide for Ransomware Attack Recovery
Detaching your device might seem easy, however it is very important to do it properly. Here’s how you can do it step-by-step:
1. Unplug the Ethernet Cable or Turn Off Your Wi-Fi
If you are using a wired connection (Ethernet), unplugging the Ethernet cable will disconnect your gadget from the internet instantly. Merely turn off your router or disable Wi-Fi on your device if you’re on Wi-Fi.
- Example: Imagine you’re sitting at your desk, and you see that all your files are all of a sudden secured with odd file extensions (like.crypt or.locked). Your very first instinct needs to be to disconnect your laptop computer’s Ethernet cable television or switch off the Wi-Fi. This will avoid the ransomware from continuing to interact with the aggressor’s server, which is necessary for recover from a ransomware attack.
How to disable Wi-Fi on your laptop (Windows example):
- Click on the Wi-Fi icon in the system tray (bottom-right corner of your screen).
- Select “Disconnect” or toggle off the Wi-Fi option to cut the connection.
- On macOS, click the Wi-Fi symbol in the top-right menu bar and choose “Turn Wi-Fi Off”.
2. Eliminate Any External Drives (USB, Hard Drives, and so on).
Detach them instantly if you have any USB drives, external difficult drives, or flash drives connected to your gadget. Ransomware can contaminate these drives much like it can with your primary device, which might lead to your backup data being jeopardized too. Detaching them is an important part of your ransomware disaster healing plan.
- Example: Let’s say you have an external hard disk drive plugged into your laptop computer, believing it’s a safe location to keep essential files. If your laptop computer gets infected, ransomware can infect that external drive and secure your backups, making it impossible to recover files later. Disconnecting the disk drive before it gets infected is a critical relocation in your ransomware healing plan.
How to safely eject an external drive (Windows example):
- Click the “USB” icon in the system tray (bottom-right).
- Choose “Eject [Device Name]”.
- Physically unplug the external device from your laptop.
3. Shut off Your Device Completely if You Can’t Disconnect Manually.
If you’re not able to disconnect your laptop from the network manually or it’s difficult to access the Wi-Fi/connection settings in time, closing down the device completely is the most safe next step. This assists in the recover from a ransomware attack process by stopping the infection before it can spread out.
- Example: Let’s state your gadget has ended up being unresponsive due to the fact that the ransomware is running in the background and taking in all resources. Powering off the device will stop the malware from continuing its work if you can’t access the settings to detach Wi-Fi or unplug cable televisions.
How to turn off your device (Windows example):
- Press and hold the Power button on your laptop or desktop.
- Select Shut down from the options that appear, or hold the power button until the device completely powers off.
For Mac:
- Press and hold the Power button (or Touch ID on newer models) until the shutdown options appear.
- Click Shut Down to turn off your Mac.
Why Disconnecting Quickly Can Save You Time and Data in Ransomware Disaster Recovery?
Real-Life Scenario: Let’s state you run a little business and your accounting software gets locked by ransomware. If your laptop computer is still connected to the network, the attacker could possibly spread the ransomware to your file server, where you store all your service data.
By simply interfering with the ransomware’s communication with its remote servers and avoiding the infection from spreading out to other gadgets. You may be able to protect a large part of your system intact as part of your ransomware attack healing.
Key Takeaways from Step 1:
- Detach from the Network Immediately: Unplug your Ethernet cable or switch off your Wi-Fi. This stops the ransomware from infecting other gadgets, a key part of recover from a ransomware attack.
- Eliminate External Devices: Unplug any USB drives or external difficult drives, as these can be contaminated by ransomware too.
- Turn Off Your Device: If you can’t stop the infection or disconnect, switching off your gadget will halt the ransomware’s process and give you time to figure out the next actions for ransomware recovery.
By following these basic steps, you buy yourself time to take additional action without making the circumstance worse, adding to your general recover from a ransomware attack.
Next Step: After detaching, you’ll need to evaluate the situation and collect details about the kind of ransomware you’re dealing with. But disconnecting your devices right away is the most essential first action to take when you suspect a ransomware attack, specifically in the recover from a ransomware attack.
When you initially presume a ransomware attack, detaching your contaminated device from the internet and your regional network is your first top priority. Many ransomware strains look for connected devices or drives to contaminate, triggering more damage the longer they have access to your system. Recover from a ransomware attack is just possible if you take quick action to isolate the contaminated device.
The objective of disconnecting is to stop the ransomware from continuing to spread and encrypt more files, conserving your information from further damage and contributing to your ransomware catastrophe healing.
Ransomware can infect these drives just like it can with your primary device, which might lead to your backup data being compromised too.
Note: Building a Secure Remote Workforce: Cybersecurity Practices You Should Implement
Step 2: Don’t pay the ransom.

If ransomware encrypts your files, the people who want to get them back will usually want a ransom in return for opening them. If you’re under a lot of stress and need to get to important files right away. It might be tempting to pay the ransom and get your files back as soon as possible. But paying the ransom is not an option. It can make things worse.
Why You Shouldn’t Pay the Ransom to Recover From a Ransomware Attack
Paying the ransom might seem like the easiest or fastest way to get your files back. ut it doesn’t mean that your files will be decrypted or that the attackers will keep their word.
The problem is that there is no guarantee that the opponents will really unlock your files after you pay. Some victims have said they paid the ransom but never got the secret to decrypt the files. Others have been targeted again by the same criminals.
Here are some reasons why paying the ransom isn’t a good or safe choice:
- No Guarantee of Decryption: If you pay, the bad guys might not give you the decryption key or they might send you a key that doesn’t work.
- Encourages Criminal Activity: Paying the ransom gives the cybercriminals money, which makes it much easier for them to keep doing illegal things. This makes it more likely that more attacks will happen, both on you and on other people.
- You Could Be Targeted Again: If your enemies know you’re willing to pay, they might go after you again in the future or give your information to other criminals. It basically puts a target on your back.
The Effects of Paying the Ransom
Not only is paying the ransom a bad idea because it doesn’t guarantee results. It can also make things worse:
For example, picture yourself as the owner of a small business who pays the ransom because you think it will get your important customer data back. You notice that your system is running slower than usual in the days after you made the payment. You learn that the attackers have been watching your network and taking more data. You gave these criminals money by paying the ransom, and now they may be able to launch more attacks.
Case Study: After paying the ransom for their encrypted files, one company was hit by a second ransomware attack just a few weeks later. The criminals used the first payment to pay for more attacks, and the company lost money and information again.
What to Do After You Decide Not to Pay
Your next steps are very important for getting your files back and keeping your systems safe from more damage now that you’ve decided not to pay the ransom. This is what you need to focus on:
- Separate the Infected Systems: Make sure that the infected systems are not connected to the rest of your network. This keeps the ransomware from spreading even more.
- Scan for Ransomware: Use updated antivirus software to do a full system scan and find and get rid of any remaining traces of ransomware.
- Restore from Backups: If you have reliable backups, use them to restore your systems and make sure they don’t have any ransomware on them.
Not paying the ransom not only protects you from future attacks, but it also helps fight the bigger problem of ransomware. The fewer people who pay, the fewer resources cybercriminals will have to keep attacking.
What You Should Know About Recover From a Ransomware Attack:
- Don’t pay the ransom: Paying doesn’t mean your files will be unlocked, and it gives hackers money for future attacks.
- Use Backups: If you have them, restore your files from backups, which can be either offline or in the cloud.
- Find Decryption Tools: Visit websites like No More Ransom to get free decryption tools for your ransomware problem.
- Get Professional Help: If you can’t get your files back on your own, call a cybersecurity expert for help.
Why You Shouldn’t Pay
In short, paying the ransom is not only a useless service. It could also make your system more vulnerable and lead to more attacks. Instead of paying, focus on reliable recovery methods like backups or decryption tools, and get help from professionals when you need it.
If you’re under a lot of stress and need to get to important files right away, paying the ransom and getting your files back as soon as possible might be tempting. The service does not include paying the ransom. Some victims say they paid the ransom but never got the decryption key, while others say the same criminals have gone after them again.
For example, picture yourself as a small business owner who pays the ransom because you think it will get your important customer data back. By paying the ransom, you’ve given these criminals money and may have opened the door to more attacks.
Step 3: Look at the Ransomware Message or Ransom Keep In Mind

When ransomware secure your files, individuals who did it will frequently leave a ransom note or message on your device. This message normally has crucial information about the attack and tells you how to pay the ransom to get your files back. The ransom note might appear frightening. But it can likewise offer you crucial information that can help you find out what kind of ransomware you’re handling and what to do next.
Why It’s Important to Look at the Ransom Note
The ransom note is the very first thing you obtain from the enemies, and it can offer you helpful details. You can typically figure out what the note indicates by taking a look at it closely.
- The type of ransomware that has actually entered your gadget.
- The opponent’s needs, such as just how much money they desire and how they want it paid.
- Any details that could assist you discover the assailant or find out why they did what they did.
- Knowing this information will assist you decide what to do next, like whether you can get your data back without paying or if you need to get expert aid.
What to Look for in the Ransom Note
Here are the most crucial things to look for in the ransom note recover from a ransomware attack:
- Submit Name or Extension
The file extension or name that the ransomware contributes to your encrypted files is among the most useful pieces of info in the ransom note.
Why this is necessary: The file extension is often connected to a specific kind of ransomware. If you understand what the extension is, you can figure out what type of ransomware it is faster and look for specific tools, like decryption tools or recover from a ransomware attack guides.
if you see that your files now have extensions like.crypt. locky, or.cerber, these are indications of the type of ransomware you have.
Crypt could be connected to the CryptoLocker ransomware.
Locky recommends that Locky ransomware is assaulting
. cerber show The Cerber ransomware.
Example in Action: You see that your files, like report.docx and photo.jpg, have changed to photo.jpg.locky and report.docx.locky. The.locky extension right away tells you that Locky ransomware has actually attacked your system. This lets you try to find Locky decryption tools or options that specify to that pressure.
- How to Pay
Ransomware assaulters typically request for cash to let you get back to your files, and this is usually explained in the ransom note. The note will state:
- The quantity of cash required (often in Bitcoin or other cryptocurrencies).
- The address of the cryptocurrency wallet where the payment requires to go.
- The deadline for payment before the ransom increases or the files are lost.
Why this is so essential: Knowing what the aggressors desire in terms of payment can assist you understand what they want, which can help you choose whether to pay or try to recover from a ransomware attack in other methods.
Example in Action:
The ransom note says, “Send 1 Bitcoin to this address: 1A2B3C4D5E6F7G8H9I0J within 72 hours.” The rate will double after that. If you don’t pay, your files will be completely erased. This gives you some essential details:
- The ransom amount is one Bitcoin, which deserves thousands of dollars today.
- The individuals you are battling want payment within 72 hours.
- If you don’t pay, it’s clear what will happen: your files might be lost permanently.
It’s generally best not to pay. But understanding the payment information can help you look at the circumstance and choose what to do, like calling cybersecurity professionals or looking for decryption tools for your specific ransomware.
- Details on how to contact us or speak to someone
Some ransom notes will give you a way to connect with the people who are holding you captive. This could be in the form of:
- A chat service or e-mail address for talking to each other.
- A link to a website where you can pay the ransom or get more help.
- A “proof of life” sample, where the aggressors state they can open your files by decrypting a little file.
Why this is so important: These contact numbers can help you find out more about who the aggressors are and if the ransomware becomes part of a bigger criminal activity ring. They can also assist you understand how to pay, however it’s essential not to talk to the enemies directly, as this could put you in much more danger.
Example in Use:
Your ransom note may state something like:
” Email us at support@ransomwareattack.com to get your files back.” We will inform you how to pay. Do not try to reach us by any other means, or your files will be deleted.
This offers you:
A method to get in touch (email) that might help identify the assailants or learn where the attack happened.
A clear indication of how to happen with the payment and unlocking process (but remember that paying is not a good idea).
However speaking to the attackers could make your security even worse. It is more secure to try to find other ways to heal, like decryption tools or professional aid.
Why is it crucial to look at the ransom note?
You need to check out the ransom note thoroughly due to the fact that it consists of essential details that can help you make choices. Rather of freaking out or succumbing to your challengers, you can:
- Discover what kind of ransomware it is and search for specific decryption tools.
- Know exactly for how long you have before the ransom increases or your files are lost.
- Do not pay the ransom; instead, concentrate on safer methods to heal, like backups or getting help from professionals.
You might discover that there is an entirely complimentary decryption tool offered for the particular kind of ransomware that has assaulted you sometimes.
Crucial Points from Step 3:
- Search for the file type: This is generally the most convenient method to discover just how much pressure the ransomware is putting on you.
- Read the guidelines for payment thoroughly: Know what the attackers want, however do not pay.
- Find out how to contact us: This can in some cases help you determine who the assaulter is, however it’s more secure not to speak to them directly.
- Utilize the details to try to find tools that can decrypt: Find out what type of ransomware it is and see if you can get your files back without paying the ransom.
Why This Step Is So Important for Recover From a Ransomware Attack
You can learn a lot about the kind of attack you’re handling, the amount of ransom, and any possible possibilities of healing by looking at the ransom note. With this info, you can with confidence select what to do next and move toward restoring your information in a safe and ethical method.
When ransomware secure your files, the criminals will typically leave a ransom note or message on your gadget. This message typically has important information about the attack and informs you how to pay the ransom to get your files back. The ransom note may seem scar. But it can likewise provide you essential information that will help you find out what sort of ransomware you have and what to do next.
The.locky extension lets you understand right now that Locky ransomware has attacked your system, so you can try to find Locky decryption tools or options that deal with that strain.
When you open the ransom note, it states, “Send 1 Bitcoin to this address: 1A2B3C4D5E6F7G8H9I0J within 72 hours.”
When ransomware locks up your files, the individuals who did it will typically leave a ransom note or message on your device. This message generally has essential info about the attack and informs you how to pay the ransom to get your files back. The ransom note may seem scary. However it can likewise give you crucial info that can help you figure out what type of ransomware you’re dealing with and what to do next.
When ransomware locks up your files, the criminals will typically leave a ransom note or message on your gadget. The ransom note might appear frightening. However it can also offer you essential info that will help you figure out what kind of ransomware you have and what to do next.
Step 4: Discover what kind of ransomware it is
After checking out the ransom note and collecting any information you can about the ransomware attack, your next step is to find out what the particular stress of the ransomware is. Because the type of ransomware you have will have a huge effect on what you do next to get your computer system back up and running, this action is very important.
Some kinds of ransomware have easy-to-find decryption tools, while others may need various ways to get much better. You can focus on the very best ways to get your data back if you understand what the stress is.
Why It’s Important to Find the Strain
Finding the ransomware stress is necessary for the following reasons:
- Decryption Tools: Some ransomware, like WannaCry or CryptoLocker, have made public decryption tools that can help you get your files back without paying the ransom. However these tools only work well for particular kinds of tension.
- Healing Strategy: The way to recover from ransomware depends on the type of ransomware. If you’re handling a popular pressure, you may have a great deal of methods to recover, like decryption tools, system bring back points, or backups. For newer or less common tension, there might not be any trusted ways to get better without professional aid.
- Discovering the Right Solution: Different kinds of ransomware stress act in different ways. Some encrypt files, some lock your entire system, and some may even take your information. Knowing what pressure you’re dealing with assists you prevent losing time and concentrate on the very best option.
How to Find the Ransomware Strain
There are a few various ways to tell if ransomware has really infected your system. These are the most trustworthy ways:
- Using online tools
There are many complimentary, trusted online tools that can assist you determine the ransomware tension level based upon the ransom note or encrypted files.
ID Ransomware: You can submit either the ransom note or an encrypted file using this online tool. It examines the file against known ransomware pressures to see if it matches.
How to use ID Ransomware:
- Go to the site: ID Ransomware.
- Choose in between putting out the ransom note or an encrypted file.
The tool will try to match the ransomware to a known pressure if you follow the directions.
Example in Real Life:
You get a ransom note with a file extension like.cerber. You send it to ID Ransomware, which sees it as Cerber ransomware. This lets you try to find decryption tools that can assist you with that.
No More Ransom is another excellent tool for fighting and figuring out ransomware. The police and cybersecurity companies interact to distribute totally free decryption tools for a lot of various types of ransomware.
How to use No More Ransom:
- Take a look at No More Ransom.
- Go to the “Decryption Tools” area.
You can either browse the list of easy-to-find decryption tools or utilize the “Ransomware Identification” page to help you determine what the pressure is.
In Practice:
If the ID Ransomware tool sees your ransomware as CryptoLocker, you can go to No More Ransom to see if they have a free decryption tool you can download.
- Look at the File Extensions
A lot of ransomware adds special file extensions to the files it secures. These extensions are a really essential hint for determining the pressure.
Typical file extensions for ransomware are:
Example in Real Life:
You learn that your files have actually been relabelled from importantfile.docx to importantfile.docx.locky. This extension informs you that the Locky ransomware is involved, and then you can try to find decryption tools or healing services that specify to Locky.
- Check out the ransom note for ideas.
Some ransom notes have info that assists you determine what kind of pressure you’re under. These could be the name of the ransomware, the variation number, or the specific language and payment directions that are linked to understood ransomware groups.
For instance:
You might see something like this in a ransom note: “Send 1 Bitcoin to 1A2B3C4D5E6F7G8H9I0J within 48 hours to get your files back.” This is an attack by WannaCry. Here, the WannaCry strain is clearly revealed, which lets you focus your recovery efforts on tools that can decrypt WannaCry.
Why knowing the kind of ransomware assists you get your files back.
- Gave away tools for decrypting.
Scientists have actually checked out and studied some ransomware pressures, like CryptoLocker and TeslaCrypt. This means that free decryption tools are offered for these strains. If you understand what the stress is, you can find these tools and get your files back without paying the ransom.
For example, if you discover that the ransomware pressure is WannaCry, you can utilize the free decryption tools that are easy to find on websites like No More Ransom or Kaspersky to get your files back.
- The finest method to get much better.
When you understand what the pressure is, you’ll be much better able to choose the very best method to recover. You can use decryption tools to deal with some tension, but for others, you may need to bring back from backups or use system bring back points.
If you discover that the ransomware is Ryuk, for example, there aren’t any public decryption tools readily available, so you’ll most likely need to count on offline backups or get assist from a specialist.
- Stopping more damage.
Knowing what is triggering your stress can help you prevent losing time on healing methods that don’t work. Some kinds of ransomware stress are worse than others, and some are simpler to get over. Comprehending the strain makes sure you don’t lose time on options that do not work.
If Locky encrypts your files, you might be able to discover a decryption tool online that works. This will conserve you the problem of trying techniques that don’t deal with other pressures, like Ryuk, which does not have a known decryption tool.
What you require to understand from Step 4:
Find out what sort of ransomware is attacking your system by utilizing tools like ID Ransomware and No More Ransom.
- Find the File Extension: The file extension (like.locky or.cerber) is a really essential hint that can assist you figure out what sort of ransomware it is.
- Inspect the Ransom Note: The ransom note might have important details, like the name or variation number of the ransomware.
- Concentrate On Decryption Tools: After you understand what sort of ransomware it is, look for decryption tools or approaches that work for that type of ransomware.
Why figuring out the stress is a video game changer.
When you understand how much pressure ransomware is placing on you, you can take specific actions to get your files back and limit more damage. You can focus your efforts on the most trusted service if you know precisely what sort of pressure you’re under. This might be using a totally free decryption tool or restoring from backups.
- Recovery Strategy: Different types of ransomware have different ways to return on track. If you’re dealing with a popular stressor, you might have a great deal of methods to recover, like decryption tools, system restore points, or backups. Typical file extensions for ransomware are: Knowing that you’re under pressure can assist you prevent losing time on healing techniques that won’t work. Some types of ransomware are worse than others, and some are much easier to get rid of.
- Healing Strategy: The method to recuperate from ransomware depends on the type of ransomware. You send it to ID Ransomware, which sees it as Cerber ransomware. When you understand how much pressure ransomware is putting on you, you can take specific steps to get your files back and restrict more damage.
Note: Bug Bounty Hunter Roadmap: How to Hack Legally & Earn Your First Reward Fast
Step 5: Discover what decryption tools are out there

As soon as you understand what type of ransomware it is, the next action is to look for totally free decryption tools that can assist you get your files back without paying the ransom. Cybersecurity specialists have made totally free decryption tools for several types of ransomware that are readily available to the public. These tools can assist victims get their files back.
There might not be any decryption tools for some kinds of ransomware, like Ryuk or Maze. There are tools that can help you get your data back for complimentary for other types, like CryptoLocker, Locky, and WannaCry.
Why you need tools to decrypt
Utilizing decryption tools is among the finest ways to get back on your feet after a ransomware attack without paying the ransom. Paying the ransom is never ever an excellent concept. Rather, using decryption tools is a more secure, more moral, and more effective method to heal. These tools are expected to reverse the encryption of files, which will let you get to your files again.
You now understand that CryptoLocker is the sort of ransomware that has actually truly gotten into your system. There is a recognized decryption tool for CryptoLocker that lets you open your files without having to pay the hackers, which is a great thing. You can rapidly get your files back with the tool without having to handle individuals who did wrong.
Where to Find Tools for Decryption
These are the finest locations to find decryption tools that can assist you get your files back:
- No More Ransom
No More Ransom is a collaboration between cops and cybersecurity business that offers individuals complimentary tools to decrypt lots of types of ransomware. This platform has tools for a few of the most common kinds of ransomware and is an excellent resource for individuals who have been assaulted by ransomware.
How to utilize No More Ransom:
- See www.nomoreransom.org to get more info.
- Go to the section called “Decryption Tools.”
- Find the best ransomware tension for your attack, like Locky, CryptoLocker, or WannaCry.
- If you can quickly discover a tool, download it and follow the directions to decrypt your files.
Why No More Ransom is Needed: Professionals and law enforcement firms have actually set up a relied on source to make certain that the tools on the site are safe and work as they should.
Example in Action:
You understand that CryptoLocker secures your files. You discover out that No More Ransom has a free decryption tool. You run the tool and download it. In a couple of minutes, your files are back to how they were before you paid the ransom.
- Companies that make software to protect against infections
Numerous business that make anti-virus software also make tools that can open certain types of ransomware. Kaspersky, Bitdefender, and Emsisoft are widely known companies that make software application to secure against viruses. They usually offer these tools away for free to help people who have been harmed by ransomware.
How to discover decryption tools from a company that makes anti-virus software application:
- Go to the main site of the business that makes the anti-virus software application, like Kaspersky, Bitdefender, or Emsisoft.
- Search for their area on tools for decrypting ransomware, which is normally discovered under the “resources” or “tools” tab.
- Get the best tool for the type of ransomware you have.
- If you want to get your encrypted files back, you should thoroughly follow the steps given.
Why antivirus companies make these tools: These business are committed to stopping ransomware attacks due to the fact that they know how bad they can be for services and people. They can assist victims without charging them by providing them tools to decrypt their files.
Here is an example in action:
You know that WannaCry is the name of the ransomware, and a fast search shows you that Kaspersky has a complimentary tool to decrypt it. You can get your files back quickly and totally free by downloading the tool and scanning your computer system.
- Ransomware-only online forums or areas
Some online areas or online forums for ransomware have tools to help you decrypt files or talk about how to handle particular kinds of tension. BleepingComputer and other cybersecurity forums typically have links to tools or guides that can help with decryption.
How to utilize these online forums:
- See security forums that you can rely on, like BleepingComputer (www.bleepingcomputer.com).
- Find the ransomware that is making you nervous, such as Locky or Cerber.
- If any decryption tools or ways to recover have actually been shared, look at user reports and see what they state.
- Download the tools that are suggested and after that follow the guidelines that feature them.
Example in Action:
There is a thread on BleepingComputer about Cerber ransomware where individuals have actually even published links to a tool that can decrypt Cerber files. After you run the tool and download, you can get your encrypted files back.
When Downloading Decryption Tools, why You Should Be Careful
There are a great deal of trustworthy sites, such as No More Ransom and antivirus companies, that use safe decryption tools. However downloading tools from sites you do not trust can be hazardous. Some decryption tools might be malware that is pretending to be something else so that your system is simpler to hack.
If you download a decryption tool from a site you don’t trust or a questionable online forum, for example, the tool could be malware, which could make things even worse. Constantly get tools from sites you can trust, like No More Ransom or a well-known anti-virus business.
After you download the tool and discover to decrypt, what do you do?
Now that you’ve found the best tool for decrypting, here’s what to do next:
Get the Tool: Get the tool from a trusted site like No More Ransom, Kaspersky, or Bitdefender.
Scan Your System: After you download the tool, use it on the computer system that has the infection. The tool will browse your files and try to decrypt them.
Examine Your Files: After the tool has actually ended up decrypting your files, check to see if they are back to how they were previously. Check that the files open correctly and that they are no longer protected.
Essential Tip: Before you use any decryption tool, ensure your antivirus software application is up to date and run a complete system scan to ensure there are no other dangers on your computer.
Things to keep in mind from Step 5:
Stop getting info from sources you can’t trust Ransom, Kaspersky, Bitdefender, and Emsisoft all have great complimentary decryption tools.
- Download Safely: Always get decryption tools from relied on sources to avoid getting malware.
- Do exactly what the instructions say: Most of the time, decryption tools need you to do certain things. Make sure you read all the directions thoroughly before utilizing the tool.
- Back up your information: Before you utilize any decryption tool, you should back up your files to prevent losing much more information.
Why This Step Is Important
After a ransomware attack, among the first things you should do is search for tools that can assist you decrypt the files. If you have a decryption tool, you can rapidly get your files back without having to deal with the assaulters. This is a safe, moral, and fast way to get your information back without paying the ransom.
You’ll have a better chance of getting your files back and avoiding future ransomware hazards if you follow the actions in this guide.
Utilizing decryption tools is one of the finest methods to get your files back after a ransomware attack without paying the ransom. You can utilize a recognized decryption tool for CryptoLocker to open your files without having to pay the hackers. You go to No More Ransom and find a free tool to decrypt your files. One of the first things you ought to do is look for tools that can decrypt your files when things go back to normal after a ransomware attack. If you have a decryption tool, you can rapidly get your files back without having to handle the hackers.
You can open your files without paying the hackers with a known decryption tool for CryptoLocker. You can rapidly get your files back without needing to handle the enemies if you have a decryption tool on hand. Utilizing decryption tools is among the best ways to get your files back after a ransomware attack without paying the ransom. If you have a recognized decryption tool for CryptoLocker, you can open your files without paying the enemies. You can rapidly get your files back without having to deal with the individuals who took them if you have a decryption tool.
Once you understand what kind of ransomware it is, the next action is to look for free decryption tools that can assist you get your files back without paying the ransom. These tools are supposed to reverse the file encryption of files, which will let you get to your files again.
Utilizing decryption tools is one of the best ways to get your files back after a ransomware attack without paying the ransom. You can rapidly get your files back without having to deal with the assailants if you have a decryption tool on hand. Utilizing decryption tools is one of the best methods to get your files back after a ransomware attack without paying the ransom.
Step 6: Take a look at your backup systems.

If you’ve been proactive and followed a great backup strategy, the next thing you should do after getting hit with ransomware is examine your backup systems and restore your files. The very best method to protect yourself from ransomware is to have backups you can rely on. This way, you can get your files back without paying the ransom.
Why It’s Important to Check Your Backup Systems
If your primary information is secured after a ransomware attack, your backup systems can be a lifesaver. If you routinely back up your data, you must have the ability to quickly and easily restore your files without needing to deal with the assailants or fret about paying the ransom.
It’s insufficient to just have backups. You require to make certain that your backups are up to date, tidy, and can be restored.
The 3-2-1 Backup Rule
The 3-2-1 backup guideline is an excellent way to make sure that your information is safe from cyber hazards like ransomware. This rule states:
Three copies of your info: You must constantly have at least 3 copies of your information. The initial and two backups.
There are two various types of media: You should keep your backups on a minimum of two various kinds of media, such as a cloud storage service and an external hard disk drive. The threat of losing all copies goes down if one medium is damaged.
1 copy off-site: Always keep one backup copy off-site, like in the cloud or on a remote server, to secure versus regional hazards like ransomware. The off-site backup remains safe even if your local system is at risk.
If you use this backup method, you’ll always have numerous copies of your data that you can bring back, no matter what takes place to your primary gadget.
How to Get Back from Backups
Now that you understand how important it is to have a good backup strategy, here are some fast ways to get your files back from your backups:
- Get Files Back from Your Cloud Storage or External Backups
It’s time to get your data back if you’ve been utilizing cloud storage services like Google Drive, Dropbox, OneDrive, and others, or external disk drives.
Let’s state you utilize Google Drive to back up your crucial files. You understand that ransomware has contaminated your local system, but you have the most current variation of your files on Google Drive. Just sign in to your Google Drive account, find the files you desire to restore, and download them to your clean system.
How to get files back from the cloud (for example, Google Drive):.
- Go to Google Drive in your web browser.
- Indication in to your Google account and discover the file or folder you require to return.
- To get the file back on your device, right-click it and select Download.
If you are supporting to external hard disks:.
To stop moving any malware, unplug the external drive from the infected system and plug it into a clean or reformatted device.
Move the files you require from your backup drive to your computer.
- Use antivirus software application to scan your backup.
It’s very important to scan any files you desire to bring back from your backup with upgraded anti-virus software application. This will make sure that the backup isn’t likewise infected with ransomware or other malware.
Why you need to scan your backup:
If your backup systems or drives were linked during the attack, ransomware can get to them. Inspecting your backup files makes certain that the files you restore are safe and will not infect your system again.
Think about having a backup on an external hard drive that was linked to your computer the whole time the ransomware attack was going on. Even if the backup looks fine, you need to scan the external drive with antivirus software application before restoring anything to make certain it’s clean.
How to utilize anti-virus software application to scan your backup:.
- You can establish or open your antivirus program, like Kaspersky, Bitdefender, or Norton.
- Connect your backup gadget (USB drive, external drive, or network storage) to your computer.
- Use the antivirus software to scan the backup device all the way through.
If any threats are found, either quarantine or erase the contaminated files before proceeding with the repair work process.
Finest Ways to Use Backup Systems.
Follow these finest practices to make certain your backup systems are always all set to recover:.
Automate Backups: Use software that instantly backs up your files on a routine basis so you do not have to set it up yourself. You can set it to run once a week or as soon as a day, depending on how often your data modifications.
You can use Windows File History or cloud services like Google Drive or Dropbox to automatically back up files whenever they are changed or added.
Examine Your Backups Often: Just supporting your data isn’t enough; you must examine your backups often to make sure the files can be recuperated and are still there. You do not want to discover out that your backup is broken after you’ve been struck by ransomware.
Make sure your backups are kept off-site. Ransomware can assault connected drives or backups on a regional network. To secure yourself from a ransomware attack, ensure you keep one copy of your backup in the cloud or off-site.
What to Do If You Don’t Have Backups.
You still have alternatives if you do not have backups or your backups are likewise at threat:.
Try to find decryption tools. Some types of ransomware have decryption tools offered, such as No More Ransom.
Call a Cybersecurity Expert: If the ransomware is complicated or there isn’t a decryption tool offered, a professional cybersecurity service can assist you eliminate the malware and perhaps even get your files back.
Last Resort: You might desire to pay the ransom as a last option. Due to the fact that it does not ensure that the attacker will really unlock your files and it supports unlawful activities, this is not an excellent idea.
Important Points to Remember:.
The 3-2-1 Backup Rule states that you ought to constantly have 3 copies of your information, 2 various types of media, and one backup that is not on your computer system.
- Restore Files from Cloud or External Backups: If you have backups, use them to get your files back.
- Constantly scan your backup for malware or ransomware before restoring any files.
Set up automated backups and check them frequently: Set up automatic backups and check them from time to time to make sure your data is safe and can be restored.
Why It’s Important to Check Your Backup Systems.
Checking your backup systems is an essential step in getting back on your feet after a ransomware attack. You can get your files back without paying the ransom if you have tidy, up-to-date backups. This not only keeps you from needing to handle cybercriminals, however it also gives you a dependable way to recuperate from future attacks.
You can protect your data and lower the danger of losing it in a ransomware attack by following the 3-2-1 backup guideline and ensuring your backups are safe, secure, and scanned correctly.
For instance, you may utilize Google Drive to back up your important files. You understand that ransomware has actually gotten into your regional system, however you have the most current version of your files on Google Drive. You just sign in to your Google Drive account, look for the files you wish to return, and download them to your clean computer.
Checking your backup systems is a vital part of recuperating from a ransomware attack. You can get your files back without paying the ransom if you have tidy backups that depend on date.
If you’ve been proactive and followed a good backup plan, the next thing you ought to do after getting hit with ransomware is inspect your backup systems and restore your files. Ransomware can attack linked drives or backups on a regional network. To protect yourself from a ransomware attack, make sure you keep one copy of your backup in the cloud or off-site.
Inspecting your backup systems is a vital action in getting back on your feet after a ransomware attack. You can get your files back without paying the ransom if you have tidy, current backups.
Step 7: Start in Safe Mode

Sometimes, even after you disconnect your device from the network, ransomware or other dangerous software application can keep running and do more damage. Malware can get deep into your system and begin running as quickly as your computer launches. You might need to begin your gadget in Safe Mode to stop the ransomware from running.
Safe Mode is a way to start up Windows and macOS that just loads the most essential system files and motorists. This stops other programs, like ransomware, from running immediately.
Why it is very important to begin in Safe Mode
Disables Malware: When you start your computer in Safe Mode, just one of the most basic parts of your operating system are filled. This stops a lot of malware programs, including ransomware, from working. This gives you a clean location to attempt and work to tidy up your computer system.
You Can Get Rid of Ransomware: Booting into Safe Mode makes it much easier to run antivirus scans or eliminate malware because it stops a great deal of background processes from running.
Stops More Damage: If the ransomware is still running, starting your computer in Safe Mode can help stop it from locking more files or causing more damage while you attempt to clean it up or restore it from backups.
How to Start in Safe Mode
To get Windows and macOS to start in Safe Mode, do the following:
For Windows:
Restart your computer system:
To restart the computer system, click the Start button and then Restart. If you can’t get to the system, hold down the power button for about 10 seconds to force a reboot.
Press F8 before Windows begins:
Press the F8 key over and over once again as quickly as the computer begins to reboot. Keep doing this up until you see the Advanced Boot Options menu.
If you’re utilizing a more recent variation of Windows, like Windows 10, this method may not work since Windows launches so rapidly. In this case, do these things:
- Open the Settings menu.
- Pick Recovery from the menu for Updates and Security.
- Under Advanced start-up, click Restart Now.
As soon as your computer system restarts, click Troubleshoot, then Advanced options, then Startup Settings, and after that Restart.
Press 4 to choose Safe Mode when your computer system begins up once again.
Select Safe Mode:
The Advanced Boot Options menu has a lot of choices. Use the arrow keys to choose Safe Mode or Safe Mode with Networking if you need to fix something and get online.
Press Enter to start in Safe Mode.
Wait on the System to Boot: Windows will just load the crucial system submits that keep the ransomware from running. In the corners of the screen, it states “Safe Mode.”
Example in Use:
Follow the steps above to begin your computer system in Safe Mode. Now that you’re in Safe Mode, you can utilize your antivirus software application to scan for and eliminate the ransomware.
For Mac:
Restart your Mac:
- From the Apple menu, choice Restart.
- Press and hold the Shift secret to expose the secret:
- As quickly as your Mac reboots, press and hold the Shift key.
Hold it down up until you see the Apple logo design and the advancement bar. This suggests that your Mac is launching in Safe Mode.
To visit to your Mac:
When your Mac boots up in Safe Mode, simply log in like you usually do. You need to see the words “Safe Boot” in red in the upper right corner of your screen.
Tidy up malware:
You can now use the macOS Disk Utility or run an anti-virus scan to fix your computer system. Due to the fact that it stops background processes, Safe Mode makes it simpler to get rid of malware.
How to Use Safe Mode to Get Rid of Ransomware
Stops Ransomware from Re-infecting: Many ransomware pressures keep running in the background even after you detach from the network. By booting your computer into Safe Mode, you can clean it up and stop ransomware from running its harmful code.
Offers you a clean location to scan: You do not have to stress over malware getting in the way when your computer remains in Safe Mode You can run infection scans or use system bring back tools. It also stops the malware from hiding or stopping your anti-viruses software application from working.
Aids With Manual Removal: There may be times when you need to delete ransomware files by hand. This is much simpler in Safe Mode due to the fact that there are fewer processes running and less things that could get in the way of your cleansing.
What to Do After You Boot Up in Safe Mode.
As soon as you’ve successfully booted into Safe Mode, it’s time to tidy up your system as quickly as possible. You can do this:
- Look for viruses
To find and get rid of any signs of ransomware or other malware, open your anti-virus program and do a complete system scan. Now is a fantastic time to get a trusted program like Malwarebytes, Kaspersky, or Bitdefender and scan your computer system if you don’t currently have antivirus software.
- Manually eliminate malware (if essential).
You might have to erase the files yourself if your anti-virus software can’t eliminate the ransomware or discover it. Because this can be hard and bad if you don’t understand what to do, it’s finest to talk to an expert.
- Restore your data from a backup.
Now is the time to restore them if you have clean copies of your files (in the cloud or on an external drive). Before you bring back the backups, ensure to scan them with anti-virus software to make certain they aren’t infected.
- Use System Restore if you require to.
If you have System Restore set up on your Windows computer system, you can go back to a time before the ransomware attack. Due to the fact that there are fewer processes running in the background, this treatment is typically simpler in Safe Mode.
Things to Keep in Mind from Step 7:
When you boot your computer in Safe Mode, most malware is shut off, which makes it easier to clean your system.
Run Antivirus Scans: Use the current antivirus software application to do a complete system scan in Safe Mode to remove and find ransomware.
Restore from Backup: If your backups are tidy, inspect to see if your files are safe before restoring them.
System Restore: If you require to, utilize System Restore to go back to a time before the ransomware infection.
Why Safe Mode is Necessary for Removing Ransomware.
Booting into Safe Mode is among the finest ways to eliminate ransomware. This stops it from running and provides you a clean location to work. When you utilize Safe Mode, the malware doesn’t trouble you as much, that makes it much easier to clean your system. You can do this by running an antivirus scan, restoring files from backups, and even deleting ransomware files by hand.
This is a really essential action to stop the ransomware from doing more damage to your system and get it ready for the healing process.
In most cases, ransomware and other damaging software application can keep running and do more damage even after you detach your gadget from the network. Because malware can frequently be deeply embedded in your system and begin running as quickly as your computer system does, this is. To stop the ransomware from running, you might have to begin your device in Safe Mode.
To enter Safe Mode, follow the steps above. You can now use your anti-viruses software application to find and get rid of the ransomware, or you can use system tools like System Restore to return to a time before the infection happened.
To stop the ransomware from running, you might require to start your device in Safe Mode.
Booting into Safe Mode is one of the finest ways to get rid of ransomware. To stop the ransomware from running, you may need to start your gadget in Safe Mode.
You might need to start your gadget in Safe Mode to stop the ransomware from running.
Booting into Safe Mode is one of the finest ways to get rid of ransomware. To stop the ransomware from running, you may have to begin your gadget in Safe Mode.
Booting into Safe Mode is one of the finest methods to get rid of ransomware. To stop the ransomware from running, you may require to begin your device in Safe Mode.
Step 8: Look for malware and infections.

One of the very best things you can do to get rid of ransomware and ensure your system is tidy is to run a complete anti-virus scan when you start your computer in Safe Mode or when you believe your system is safe and secure and safe. Ransomware can leave behind hazardous files even if you’ve disconnected your gadget from the network. These files could keep harming your system.
It’s extremely crucial to use a relied on anti-virus or anti-malware program to discover and get rid of these threats.
Why You Should Always Run Antivirus and Anti-Malware Scans
Finding Remaining Malware: Ransomware does not simply lock up files; it also installs other unsafe software application, like keyloggers, trojans, or other types of ransomware. These programs can keep running in the background, taking information or doing more harm.
A scan gets rid of all malware from your system, not just ransomware. This significantly decreases the risk of getting contaminated again or facing other cyber hazards in the future.
If you try to bring back files from backups or switch on network access once again without first cleansing your system, any malware that is still on your system might screw up your recovery or infect your backups.
How to Begin the Scan
This is a step-by-step guide on how to scan your entire system with trusted anti-virus or anti-malware tools.
- Get an anti-virus or anti-malware tool that you can rely on.
Select a good anti-virus or anti-malware program to do the scan. Some well-known alternatives are:
Malwarebytes is an excellent method to eliminate and find ransomware and other kinds of malware.
Kaspersky is understood for being able to discover a lot of ransomware and other online dangers.
Bitdefender has fantastic protection versus ransomware and can discover malware that is tough to find.
If you’ve discovered ransomware like CryptoLocker, Malwarebytes, or Kaspersky can assist you discover and eliminate it, along with any other hazardous software application it might have installed.
- Download and install the antivirus software if you haven’t currently.
If you don’t already have antivirus software, get an excellent one. Downloading anti-viruses software from the main site is the very best way to keep other malware off your computer system.
Malwarebytes is where you can get Malwarebytes.
Kaspersky: Get Kaspersky.
Crucial: Always make sure you are downloading from relied on websites and authorities to avoid getting bad variations of antivirus software.
- Don’t simply do a quick scan; do a complete system scan.
When you set up your anti-viruses software application, do not choose a fast scan. A fast scan may not find all the bad files, particularly the ones that are hidden in ransomware. You require to do a full system scan to ensure that whatever is found.
A fast scan might look like it goes by faster, but it may not find malware that is concealing in system files, the computer system’s registry keys, or other less obvious places. A full system scan checks every file and part of your computer system to make sure there are no viruses left.
How to do a complete scan (for circumstances, with Malwarebytes):.
- Start Malwarebytes.
- Press the “Scan” button.
- Choose “Full Scan” from the list.
- Press “Start Scan.”.
Give the scan time to complete. It may take a couple of hours, depending upon how big your system is and how many files you require to scan.
How to do a complete scan (utilizing Kaspersky as an example):.
- Start Kaspersky.
- Click “Scan.”.
- Select “Full Scan.”.
To let Kaspersky examine your whole computer system for malware, click “Start Scan.”.
- Take a look at what the scan found.
Your antivirus tool will offer you a report on what it found after the scan is done. This may indicate:.
Ransomware was the very first piece of malware to get into your system.
Adware, spyware, or Trojan horses.
Other files or parts that the ransomware might have made that could be harmful.
If Kaspersky discovers WannaCry ransomware, it will show you precisely which files or tricks in the computer system pc registry are connected to the infection. You can then pick to delete or put these files in quarantine.
- Either erase or quarantine any malware that is discovered.
If the antivirus program finds ransomware or other bad files, it normally lets you pick in between quarantining them or deleting them.
Quarantine: This keeps the files safe from damage while still letting you do more research. Putting them in quarantine is a safe choice if you’re not sure you want to delete the files right away.
Eliminate: This eliminates all indications of the malware on your computer system. You just need to erase files if you are sure that the anti-virus program has actually found the bad ones.
What to Do If Your Antivirus Doesn’t Find Ransomware.
It might be because the anti-virus scan didn’t find the ransomware.
The ransomware is new, or the anti-virus hasn’t included it to its list of recognized risks yet.
The malware is hidden deep in your system, which makes it tough to find.
Here are some things you can do:.
Update Your Antivirus Software: Check to see if your antivirus software depends on date. Brand-new meanings come out all the time to assist people find brand-new risks.
How to get the most recent variation of Kaspersky:.
Open Kaspersky.
To look for updates, go to Settings > Update > Check for Updates.
Utilizing Extra Anti-Malware Tools: Sometimes, utilizing additional tools like Malwarebytes in addition to your antivirus software application can assist you find and eliminate hazards that your primary software application missed out on.
After the scan is ended up.
After the anti-virus scan is done and any threats have been dealt with, you need to do the following:.
Rebooting your computer makes certain that the modifications made by the anti-virus software application work as they should.
Revive from Backups: If you have clean, uninfected backups, you can now restore your files with self-confidence.
Re-enable Network Access: You can connect to your network once again if you’re sure your system is tidy. Watch your system for anything strange.
Update Your Software: Make sure that your os, anti-virus software, and system application program are all up to date so that you do not get contaminated again.
What You Need to Know.
To ensure you find all traces of ransomware and malware, always do a full system scan rather of a fast scan.
Use Trusted Antivirus Programs: Popular antivirus programs like Malwarebytes, Kaspersky, or Bitdefender can help you discover and get rid of ransomware.
Quarantine or Remove Threats: If you discover malware, either put it in quarantine to stop it from spreading out or delete it if you’re sure it’s the ransomware.
Run Multiple Scans: If your antivirus does not find the ransomware, either get a new one or utilize other programs to do a more comprehensive scan.
Why You Should Scan Your Computer for Viruses.
To ensure that no traces of ransomware are left on your system, you need to run a complete antivirus and anti-malware scan. A tidy scan will assist keep your system safe from future attacks and other dangers even after you’ve eliminated the ransomware.
Running anti-virus scans is an essential action in eliminating ransomware totally, which secures your details and ensures that healing is safe.
One of the most important things you can do to get rid of ransomware and make sure your system is tidy is to run a full anti-virus scan when you start up in Safe Mode or when you think your system is safe and safe. A quick scan may not discover all the bad files, especially the ones that are hidden in ransomware.
Step 9: Examine all of your gadgets and networked systems

Ransomware can move from one gadget or system to another that is connected to your network. When one device gets contaminated, the ransomware can spread out to other gadgets, so it’s important to examine all connected devices to make sure the infection hasn’t spread out.
Why It’s Important to Check All Devices
Ransomware Propagation: Ransomware typically attempts to spread from one contaminated device to other gadgets on your local network. They might likewise get contaminated if an external drive is connected or other networked systems share files with the contaminated device.
Making Sure Everything Is Clean: Just since one gadget is tidy does not suggest the others are safe. Other systems might still have ransomware on them if the infection has actually spread. When the network is restored, this might infect the device that has actually currently been cleaned up.
How to Look for Infections
This is how you can examine all the devices connected to your network in an orderly method:
- Examine all of your networked devices for infections
After you clean up the first device, you require to run anti-virus scans on all the other devices that are connected to the network, including computer systems, phones, tablets, and any devices that have actually shared folders. Ransomware can typically spread out quickly from one gadget to another.
You might have a desktop computer, a laptop computer, and a printer all linked to the same Wi-Fi network. There’s a possibility that the laptop that is connected to the same network might also get it if your desktop has ransomware on it. Running anti-virus scans on the laptop will help make sure it’s clean.
How to run anti-viruses scans (for instance, on Windows):.
- Start your antivirus program (for example, Kaspersky or Malwarebytes).
- Pick Full System Scan.
- Await the scan to end up, and after that get rid of any malware that was discovered.
- Do the same thing with all the other devices that are connected to the exact same network.
To inspect that the firewall program is on and run a full scan with any antivirus software application (like Bitdefender or Malwarebytes), just go to System Preferences > Security & Privacy > Firewall on macOS.
- Unplug any brand-new gadgets or systems that might be infected.
If you simply linked any brand-new devices, like USB drives, external hard disk drives, or perhaps smart devices, disconnect them immediately. When they are reconnected to the network, these gadgets could be contaminated and spread out the infection to other systems.
For example, you learn that your system is contaminated which you simply linked an external disk drive to your computer. You must unplug it right now and check it for any signs of infection before plugging it back into a clean system.
How to securely disconnect and scan devices:.
Disconnect any external drives, USB gadgets, or networked storage gadgets that are linked to your infected system to recover from a ransomware attack.
Before linking to any other systems, connect these gadgets to a tidy system and run a full anti-virus scan to look for malware.
Making Sure Everything Is Clean: Just because one device is tidy doesn’t suggest the others are safe. If the infection has spread, other systems might still have ransomware on them. When the network is restored, this could contaminate the gadget that has actually already been cleaned up.
You might have a desktop computer, a laptop, and a printer all linked to the very same Wi-Fi network. If your desktop has ransomware on it, there’s a possibility that the laptop computer that is linked to the very same network might likewise get it.
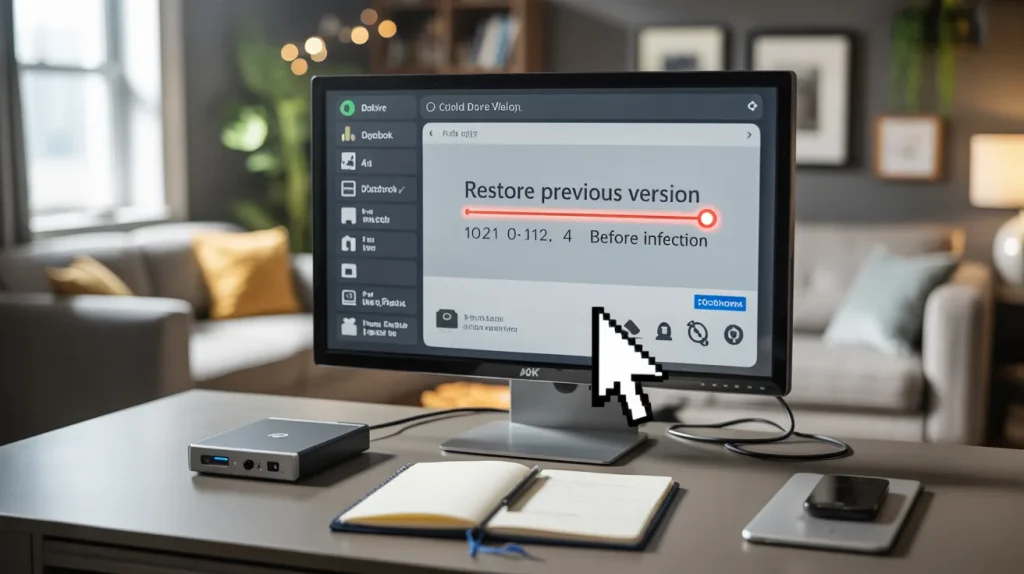
Step 10: Look for Windows System Restore Points.

You can use Windows’ System Restore feature to return to a time before the ransomware infection happened. If you have System Restore turned on, this might be a quick and easy way to undo changes made by the ransomware.
Why System Restore is so important.
Return to a clean state: If your system restore points are from before the ransomware infection and are based on date. You can go back to a time when the ransomware didn’t lock your files or cause damage.
Quick Recovery: System Restore can get your computer back up and running much faster than reinstalling the operating system or restoring from backups.
How to use the restore function.
Here’s how to use Windows’ System Restore feature:
To begin System Restore:
- Press the Windows Key and S at the same time to open the search bar.
- Type “System Restore” and then click “Make a restore point.“
- In the System Properties window, click on “System Restore.“
Choose a Restore Point:
You will see a list of restore points that the system can use. Choose a time before the ransomware attack to go back to.
Click “Next,” and then follow the on-screen instructions to get your system back to where it was.
Take a look at the Restoration:
After you confirm the repair, Windows will restart and go back to the restore point you chose.
This process might take a while, but it will undo the changes that the ransomware made.
Important: System Restore can help, but it might not always restore your files. Especially if they are encrypted. You might still need to use backups or other tools to recover from a ransomware attack by decrypting it.
Step 11: Check your cyber insurance plan

If you have cyber insurance, it might pay for some of the costs of a ransomware attack, like getting your data back, fixing your system, or even paying the ransom (but paying the ransom is not a good idea). To find out what your cyber insurance covers and how to file a claim. You should read your policy to recover from a ransomware attack.
Why You Should Read Your Cyber Insurance Policy
Financial Protection: Cyber insurance can help pay for the costs of getting back on your feet after a ransomware attack, such as hiring experts, bringing back systems, and making up for lost income.
Insurance will sometimes pay for ransom payments, but it’s best not to pay. Knowing what kind of defense you have can help you decide what to do next.
How to Make a Claim
If you have cyber insurance, you can sue by doing the following:
Call your insurance company right away:
As soon as you confirm the attack, call your insurance company so they know what’s going on.
Please let us know as much as you can, such as what kind of ransomware it is, which systems were infected, and what you’ve done so far.
Give the Right Information about recover from a ransomware attack:
The insurance company will probably need things like:
- A description of the attack.
- The type of ransomware that was used.
- Any steps that need to be taken to fix the problem, such as decrypting the data, fixing the backup, or getting help from an expert.
- The monetary effect includes the costs of healing, the time the system is down, and the ransom payment if necessary.
To make a claim, do the following:
If you call your insurance company, they will help you with the claims process right away.
Some policies might also help with the recovery process by providing legal help or forensic analysis.
Important Things to Keep in Mind from Recover From a Ransomware Attack:
Check All Devices: Scan all of the devices that are connected to your network with antivirus software to see if they have any viruses.
System Restore can help you go back to a time before the ransomware infection if you have Windows.
Check Your Cyber Insurance: Make sure your cyber insurance will help you get back on your feet after a ransomware attack. If it does, sue right away to get help with the costs.
Why These Steps Are So Important
After a ransomware attack, you should check all of your devices, use System Restore, and look at your cyber insurance coverage plan. These steps help make sure that the infection doesn’t spread any further. That you can fix your computer without any more problems, and that you have money on hand if you need it to recover from a ransomware attack.
If you follow these steps, you will have a better chance of cleaning your system and getting your files back with as little downtime and cost as possible.
Step 12: Inform the cops about the attack
Ransomware attacks are crimes. It is extremely essential to inform the right people about them. Reporting the attack can assist you recover from a ransomware attack and likewise help the police find the individuals who did it and maybe stop them from attacking other people.
Why it’s crucial to tell the authorities
- Crook Investigation: Ransomware is a kind of cybercrime, and reporting it can help the authorities discover and catch the bad guys.
- Help with Recovery: The cops can inform you what to do next, provide you resources, or even help you discover the crooks.
Who to Tell Recover From a Ransomware Attack:
Resident Law Enforcement: If ransomware has impacted you, tell your local authorities about it. They might not have the ability to get your files back, but they will compose a report.
If you are a private citizen whose files were encrypted and you didn’t have backups, you must inform the authorities so they can start a criminal investigation.
Agencies that deal with cybercrime in the United States:
In the U.S., you ought to inform the FBI’s Internet Crime Complaint Center (IC3) or the Cybersecurity and Infrastructure Security Agency (CISA) about the attack. These groups look into cybercrime and give suggestions on how to heal.
If you’re a company, tell CISA about the attack so they can assist you recover from a ransomware attack incidents.
Regulative Bodies: If you run a service that deals with sensitive information, you need to inform the ideal regulatory body (like GDPR or HIPAA) about the attack to follow information security rules.
If you’re a doctor and patient details was put at threat, you might need to tell HIPAA (Health Insurance Portability and Accountability Act) enforcement.
Step 13: Get your files back from the cloud.
If the ransomware didn’t affect your cloud services, getting files back from cloud backups is usually one of the quickest ways to get them back.
How cloud services can help you get back on your feet
Google Drive, Dropbox, and OneDrive are all cloud services that automatically back up your files. This way, you can get them back quickly after recover from a ransomware attack.
History of Changes: With many cloud services, you can change your files, which means you can go back to older versions of your files before ransomware locked them up.
How to Get Your Files Back from the Cloud
Before you try to get your data back, make sure that the ransomware has really affected your cloud account. Ensure that your cloud storage wasn’t connected to or infected.
Get back from cloud backups:
To access Google Drive, go to drive.google.com, sign in, find the file, and click Restore previous variations if you need to.
If you want to get back an older, unencrypted version of a file in Dropbox, open the file and click on Version history.
To get your files back to an earlier version, go to OneDrive online, find the files, and click Restore.
Step 14: Keep important systems off the network

To stop the ransomware from spreading to sensitive or essential systems, you might need to briefly detach those systems from the network.
Why it’s essential to keep crucial systems separate
Reduction Spread: Ransomware can spread out from one network to another. You can keep your important things safe by keeping your crucial systems different. This will stop the infection from spreading to other essential gadgets or files.
Containment: By cutting off important systems from the network, you can restrict the damage and repair the problem.
How to Keep Important Systems Apart
Unplug the Ethernet cable television TV or shut off Wi-Fi on crucial systems to disconnect from the network.
Limitation Access: If the system is still linked to the network however needs to be kept different, limitation gain access to by blocking network connections or shutting off sharing features that let people outside the network see the system.
Step 15: Make your security treatments stronger
After you overcome the attack, it’s essential to make your security stronger so that ransomware attacks do not occur once again. The next important action is to improve defenses and cybersecurity practices.
Why It’s Important to Make Your Security Stronger
Proactive Protection: Ransomware attacks typically benefit from weak security. If you make your security more powerful, you’re less likely to be attacked once again.
Safeguarding Yourself from New Threats: Ransomware is always altering, so you require to make certain your defenses are updated to secure yourself from future versions.
Important Security Steps to Take
Enable Multi-Factor Authentication (MFA): MFA includes an additional layer of security by requiring 2 or more methods to confirm something.
For example, established MFA for your email and cloud accounts so that nobody can enter into them without your approval, even if they have your password.
Establish antivirus and firewalls protection: Make sure that all of your devices have firewall softwares switched on and that their anti-viruses software depends on date.
For instance, all of the business’s computers should have antivirus software application like Malwarebytes or Kaspersky.
Apply Security Patches: To discover known security holes, you need to regularly upgrade all of your software, including running applications and systems.
Set your operating system to update itself so that you do not miss any important security spots.
Step 16: Inform Your Good Friends and Family About the Attack
If you’re a business or organization, you need to let your partners, workers, and consumers learn about the ransomware attack, particularly if it could have put delicate details at risk.
Why alerts are so crucial
Openness: It makes your clients and partners trust you more. Keeping them notified about how their details is affected ensures that they can take actions to safeguard themselves.
Risk Mitigation: It helps your contacts safeguard their own systems if their information was included.
How to Tell Contacts
Get prepared to send out an alert: Write a note that speaks about what happened, what you did about it, and how they can stay safe.
Send out the message: Use email or any other communication tools you normally utilize to get the word out.
Step 17: Consider hiring a professional service to help you get your data back after a ransomware attack.
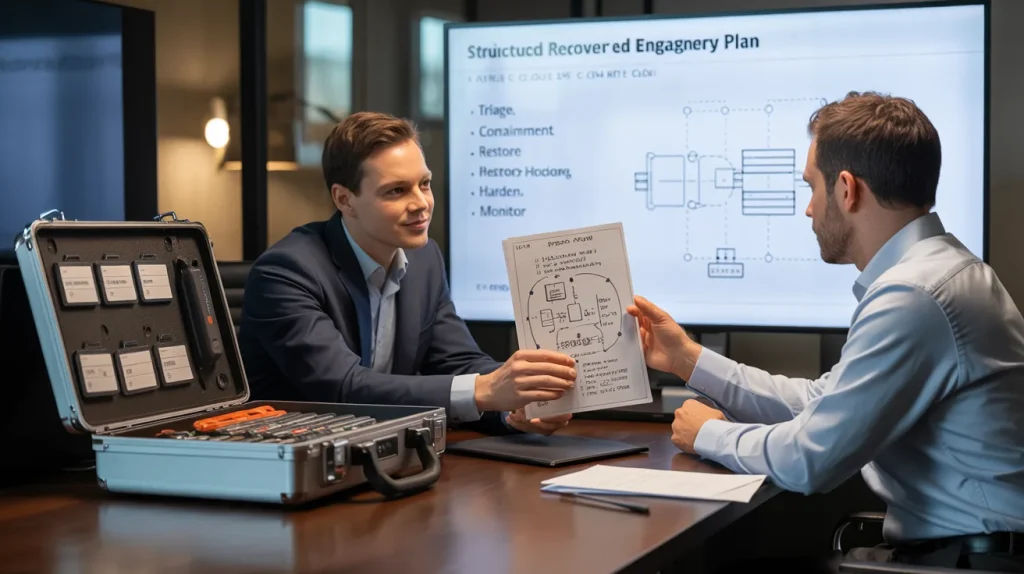
If you can’t fix the problem yourself or need professional help, it might be time to think about hiring a professional ransomware recovery service.
When You Might Need Professional Help
Getting rid of ransomware can be hard, especially when the attacks are more advanced. A specialist has the skills and tools to get out of tight spots.
Less Downtime: A healing service can help your systems get back to normal much more quickly.
How to Find Professionals For Recover From a Ransomware Attack
Find Cybersecurity Companies You Can Trust: Find a company that has a track record of helping people recover from a ransomware attack.
Look at Reviews: Read reviews online or ask for recommendations to make sure the company is honest and knows what it’s doing.
Step 18: Look for more signs of infection.

Even after you’ve cleaned your device and restored it from backups, ransomware may still try to infect it again. You need to keep an eye on everything all the time to make sure the infection doesn’t come back.
Why Monitoring Matters For Recover From a Ransomware Attack
Don’t let ransomware get into your system again. Even if it looks clean, it can often find a way to do so.
Early Detection: If you watch things all the time, you might notice strange habits or system slowdowns that could mean malware or ransomware.
- Signs that you’re getting sick again
- A lot of CPU usage or a system that runs slowly.
- Files acting strangely, like seeming to be encrypted again or getting new ransom messages.
- Repeated demands for ransom from the same or similar enemies.
Step 19: Write a new or much better plan for recovering from a ransomware disaster.
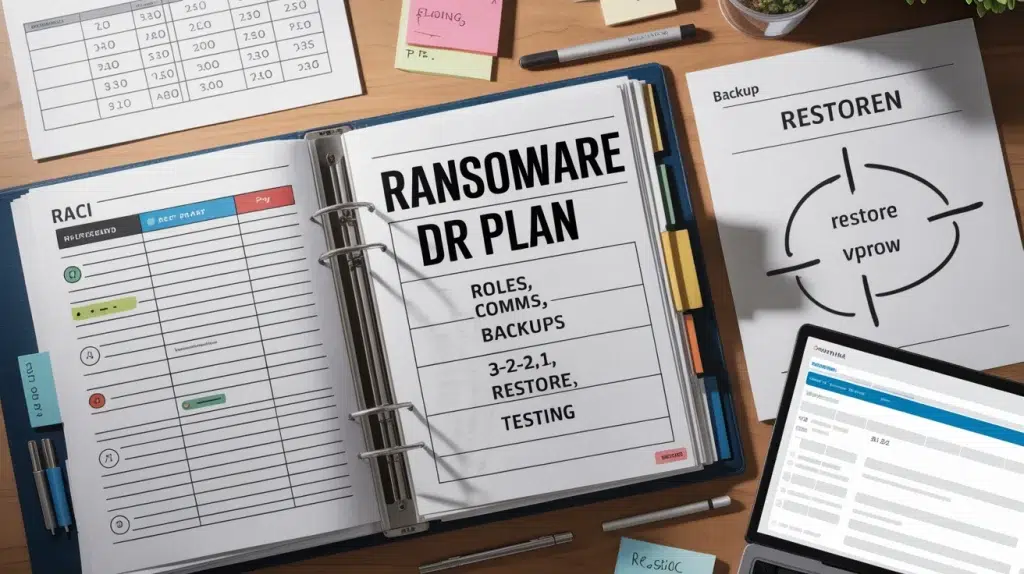
If your company or system gets hit by ransomware, a ransomware disaster recovery plan tells you what to do. It’s necessary to be ready.
Why you need a plan for getting back on your feet after a disaster.
Preparedness: A full recover from a ransomware attack plan makes sure that everyone knows what to do if they get hit by ransomware.
Less Damage: When the steps are clear, an attack does less damage and it takes less time to get back to normal.
Things You Might Not Know About a Recovery Plan
To make sure your backups happen often and follow the 3-2-1 rule, set up regular backup schedules.
Designated Response Teams: Give your employees clear tasks, such as who will talk to customers and who will handle technical recovery.
Clear Communication Protocols: Make sure there are clear ways for people to report and fix problems with ransomware.
Step 20: Teach your family or workers how to prevent ransomware.

Because individuals do things like clicking on links in phishing emails that look suspicious, Ransomware usually works. If you teach people how to remain safe from ransomware, it will be much less likely that an attack will work.
Why it is important to learn recover from a ransomware attack
Avoidance: Teaching member of the family or employees how to identify phishing e-mails and keep away from suspicious-looking attachments can decrease the threat of getting ransomware.
Security Culture: Making sure everyone understands about and looks out for threats is how to produce a culture of cybersecurity at home or at work.
Things you should teach your family or workers
How to Spot Phishing Emails: Teach people how to tell if an e-mail is fake by searching for weird attachments or senders they don’t understand.
Program individuals how to use the web securely, such as by not going to sites that look fishy or downloading files from locations they do not trust.
Take care with links that you didn’t ask for, especially those in e-mails or on social networks.
In conclusion, here are some ways to recover from a ransomware attack in the future.
You can return on your feet after a ransomware attack, if you do the right things and act quickly. You can get your data back and stop future attacks by disconnecting contaminated gadgets, utilizing backups, and decryption tools.
You ought to take strong steps to recover from a ransomware attack and information, back up your files often, and have a plan for how to recuperate from a disaster. You can be sure that your systems will remain sound and safe and that you will be all set for any future cyber threats by doing these things.
If you require aid getting back on your feet after a ransomware attack or making a strategy to recover from a disaster, please call us today. Our experts can stroll you through the actions and assist you keep your details safe in the future.

